PHISHING_CORE
🌐REAL_BROWSER_RENDERING
Docker-isolated Chrome containers render targets in real-time. No outdated templates — always pixel-perfect clones of any website.
🎯UNIVERSAL_TARGETING
Clone any site instantly: Google, Microsoft, Facebook, Instagram, banking portals, corporate SSO, crypto wallets — all supported.
🔐2FA / MFA_BYPASS
Real-time session hijacking captures authentication tokens, cookies, and 2FA codes as the victim types. Complete account takeover capability.
🔑CREDENTIAL_CAPTURE
Advanced form interception + extension + DOM: usernames, passwords, cards, SSNs, and custom fields. OTP/SMS tokens after login.
🍪COOKIE_STEALING
Extract session cookies (Netscape export). Import into your browser — bypass login with stolen auth tokens.
⌨️KEYLOGGER_CAPTURE
Every keystroke in real-time: passwords, messages, sensitive input. Field-aware detection (user / pass / OTP) with TAB/ENTER context.
💳PAYMENT_HARVESTING
Modules tuned for cards, crypto wallet flows, bank logins, and checkout fields — capture payment-related data alongside credentials.
📧EMAIL_HARVESTING
Collect emails and contacts from flows and forms. Feed follow-up campaigns and recipient groups (CSV / lists).
LIVE_MONITORING
🖥️LIVE_SCREEN_VIEW
Watch the victim's browser screen live via noVNC — exactly what they see on the phishing session, streamed to your panel.
👁️SESSION_MONITORING
Live view of interactions: keystrokes, clicks, navigation, and form activity as they happen — tied to session timeline.
📹SESSION_RECORDING
Capture sequences from live screen + exported artifacts. Review sessions step-by-step for analysis and evidence-style playback.
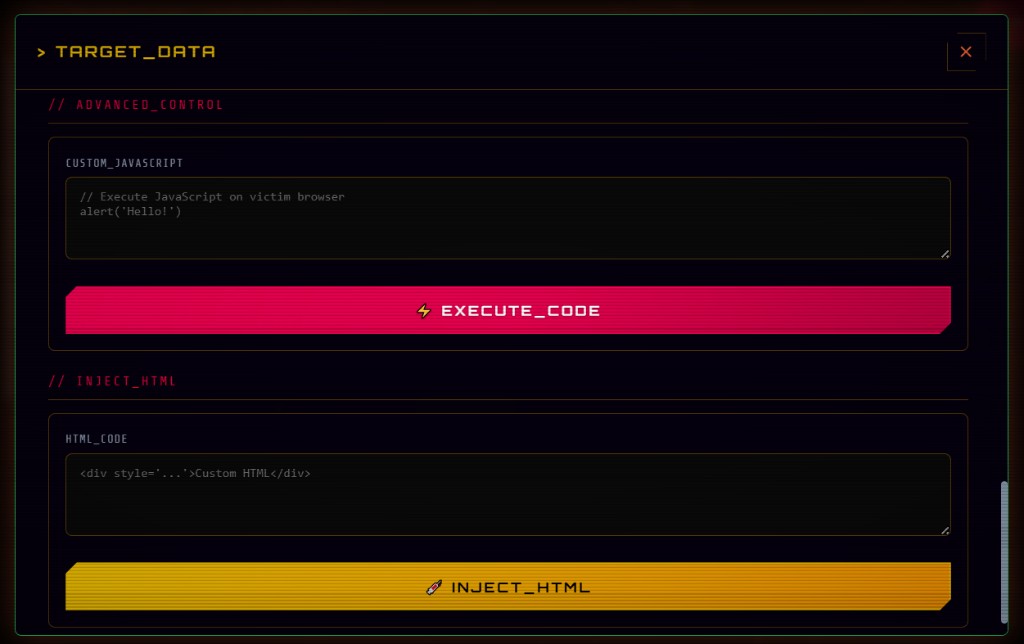
🎮BROWSER_CONTROL
Full remote control: redirect, inject HTML, fake alerts/notifications, dialogs, and execute JS in the victim browser in real time.
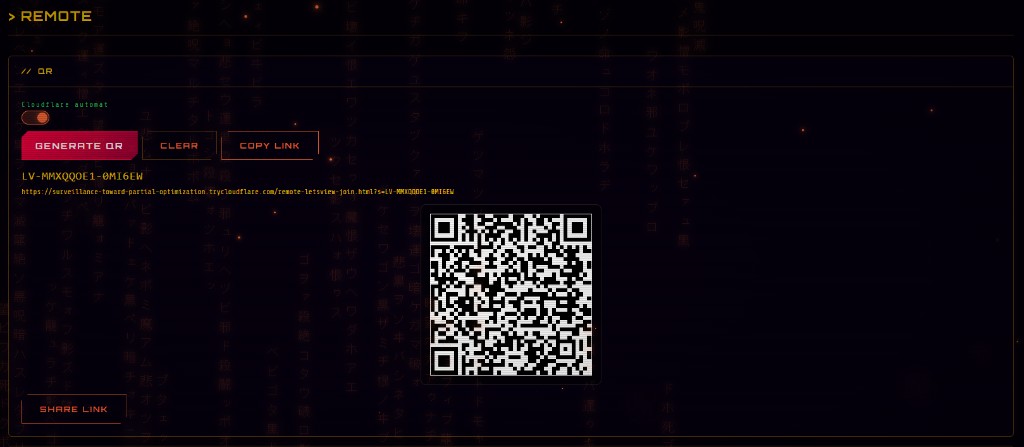
📱REMOTE_SCREEN (QR)
QR-based phone screen sharing via WebRTC. Auto Cloudflare tunnel. View the device screen from anywhere.
DASHBOARD & ANALYTICS
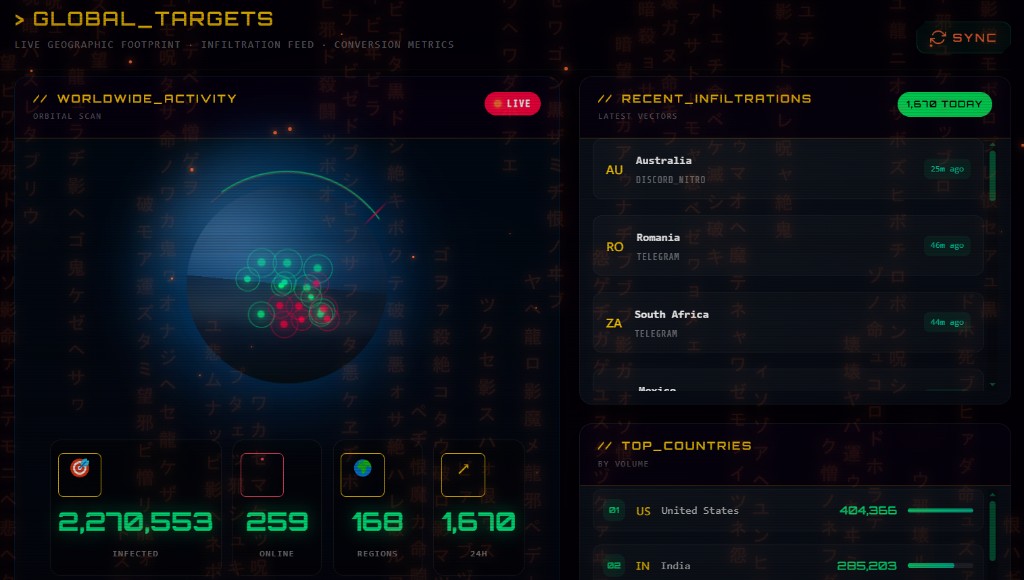
📊LIVE_DASHBOARD
Real-time command center: visitors, active sessions, credential feed, shields, and campaign metrics in one place.
📈CAMPAIGN_ANALYTICS
Visits, conversions, geography, devices, email opens/clicks, fake-update funnels — stats and timelines per campaign.
🗺️GEO_TRACKING
IP geolocation on hits, globe map, FIND_ME GPS links, and configurable geo-allowlists to shape who reaches your lure.
EMAIL_ENGINE
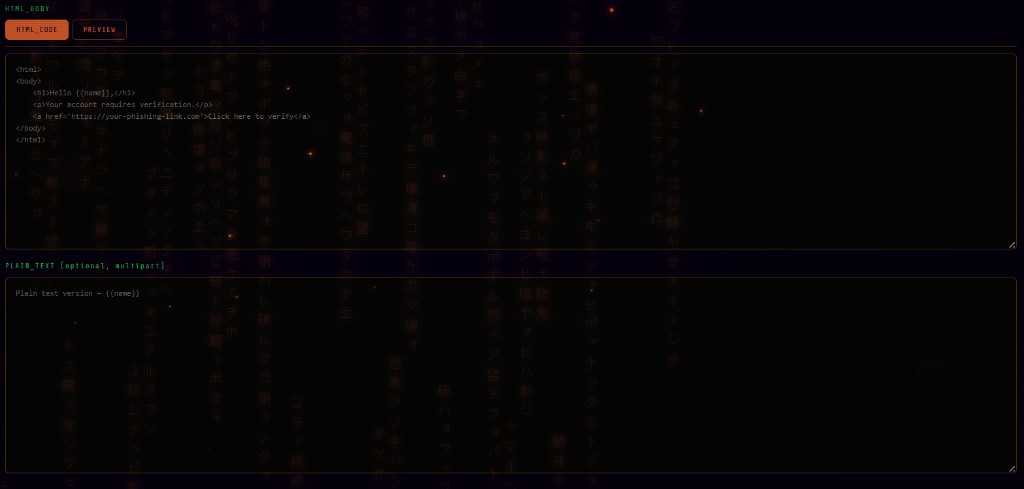
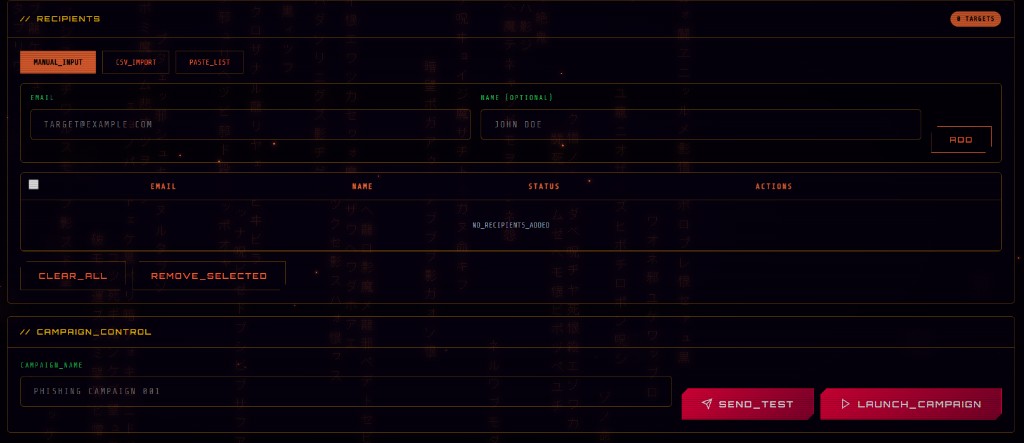
NEW📧BULK_EMAIL_ENGINE
Full campaign system: SMTP config, rate limiting, retry, CC/BCC, spoofed From, preheader injection, custom headers.
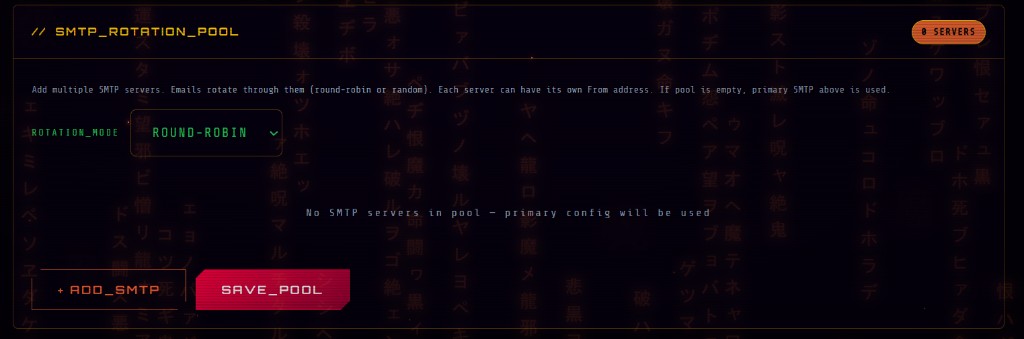
NEW🔄SMTP_ROTATION_POOL
Multiple SMTP servers rotating per email (round-robin or random). Each with own From address. Maximize inbox delivery.
NEW👁️EMAIL_OPEN_TRACKING
Invisible 1px pixel auto-injected per recipient. Know who opened, when, from which IP and device.
NEW🔗CLICK_TRACKING
Every link rewritten with unique tracking ID. See who clicked, with IP + UA, then seamless redirect.
NEW📊CAMPAIGN_TIMELINE
Full event log: Created → Sent → Opened → Clicked → Submitted. Per-recipient stats.
NEW👥TARGET_GROUPS + CSV
Save reusable contact lists. Import CSV. Select a group to populate recipients instantly.
FAKE_UPDATES & PAYLOADS
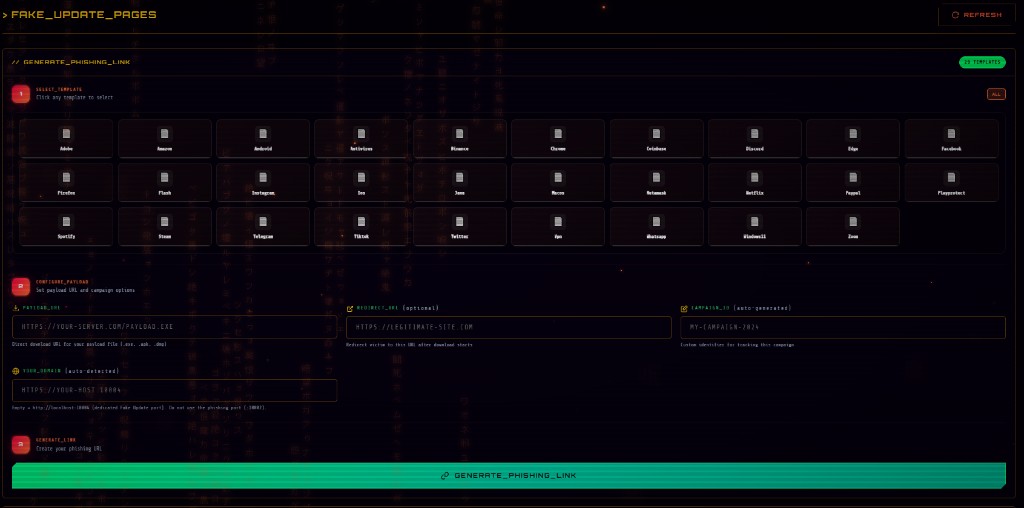
⚠️29+ FAKE_UPDATES
Chrome, Firefox, Edge, Windows 11, macOS, Android, iOS, Zoom, Discord, Steam, Spotify, Netflix, WhatsApp, Telegram, PayPal, Coinbase, MetaMask, Binance…
NEW📄FAKE_UPDATE_TEMPLATES
Pre-built fake software update pages (Chrome, Firefox, Windows, Adobe, Java & more). One-click style deployment with view/click/download tracking.
📈PAYLOAD_TRACKING
Track page views, download clicks, completed downloads. QR code generation. Custom payload URL + redirect.
FIND_ME — LOCATION
NEW📍GPS_TRACKER
Generate tracking links via Cloudflare tunnel. Auto IP geolocation + optional GPS. Satellite map in panel with full history.
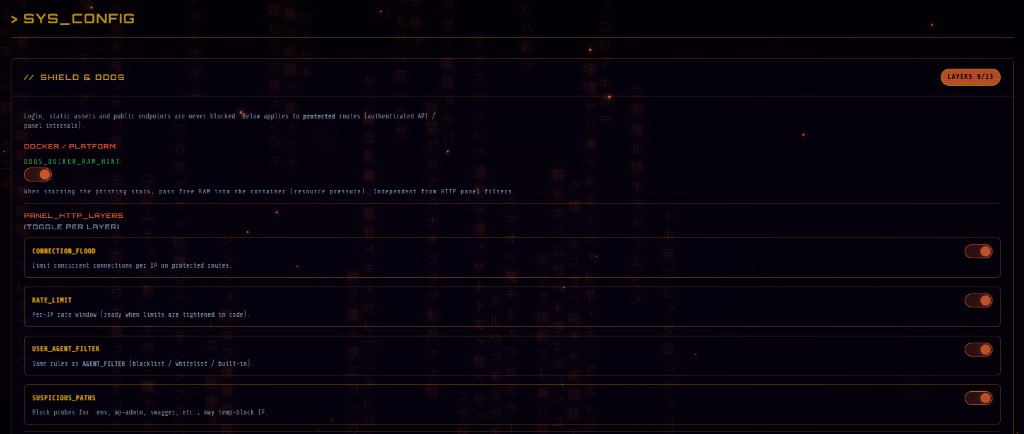
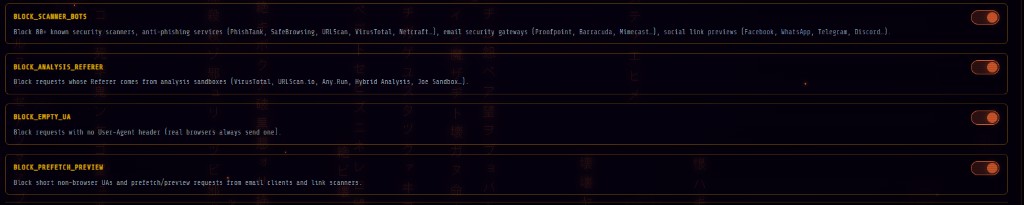
PROTECTION — 13 LAYERS
🛡️ANTI_DETECTION_SYSTEM
Multi-layer defense: UA/referer blocks, scanner & bot patterns, header fingerprinting, geo & IP reputation, burn links, JS challenge — reduce sandbox and crawler hits.
NEW⚙️13-LAYER_SHIELD
Toggle per layer: connection flood, rate limit, UA filter, suspicious paths, scanner bots, referer blacklist, empty UA, prefetch, header fingerprint, geo-blocking, IP reputation, burn links, JS challenge.
🌍GEO_BLOCKING
Allow only specific countries. Block scanners from US/IE/DE/NL. IP-based, cached.
🔥BURN_LINKS
Limit unique visitors per link. After N IPs the link dies. Prevents VirusTotal rescans.
🧪JS_CHALLENGE
Intermediate page requiring JavaScript. Bots (curl, wget, scanners) fail. Real browsers pass in <1s.
🏢IP_REPUTATION
Block datacenter IPs (AWS, Azure, GCP…), VPNs (NordVPN, Mullvad…), and Tor exit nodes automatically.
URL_MASKING
🔗URL_MASKING
Advanced obfuscation: @-trick URLs, shorteners (TinyURL, is.gd, v.gd), and parameters that make lures look legitimate.
INFRASTRUCTURE & DEPLOY
🚀INSTANT_DEPLOYMENT
One-click phishing stack: Docker session, Go resolver, nginx front — operational in minutes on your VPS.
🔒AUTO_SSL_HTTPS
TLS-ready setup via reverse proxy / your certs — phishing pages served over HTTPS like production apps.
⚙️NGINX_ROUTING
Professional reverse proxy in-container: rewrite rules, static layers, and first-line bot filtering before your lure.
🐳DOCKER_ISOLATION
Each session in its own container (4GB max, dynamic). Clean separation, no cross-talk, easy teardown.
☁️CLOUDFLARE_TUNNELS
Quick tunnels for REMOTE, FIND_ME, and panel access when you need public URLs without manual port mapping.
📱MOBILE_RESPONSIVE
Targets see real browser clones — desktop, tablet, and mobile layouts follow the original site behavior.
🔐TOTP_AUTHENTICATION
Military-grade TOTP for panel login (Google Authenticator / Authy). No stored passwords — per-operator 2FA.
🔔TELEGRAM_ALERTS
Your bot token + chat ID — instant alerts for credentials, new sessions, and critical events.
📲MOBILE_NOTIFICATIONS
Pair Telegram (and future push hooks) so hits reach your phone instantly wherever you are.
📬EMAIL_REPORTS
Campaign exports + tracking — summarize opens/clicks/recipients; pipe summaries to your inbox from your SMTP.
🗺️GLOBAL_TARGETS_MAP
Live globe: infected targets by country, feed, and geographic analytics.
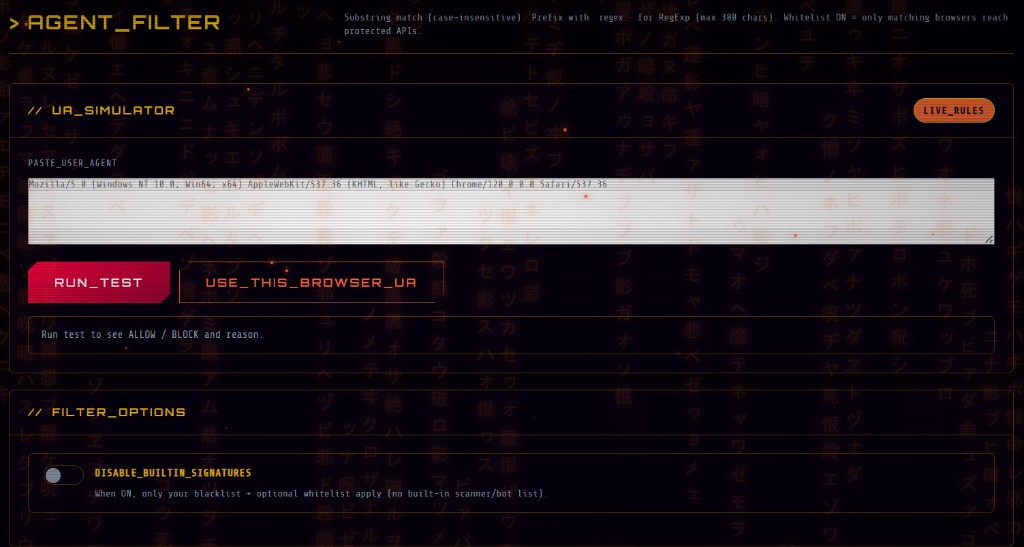
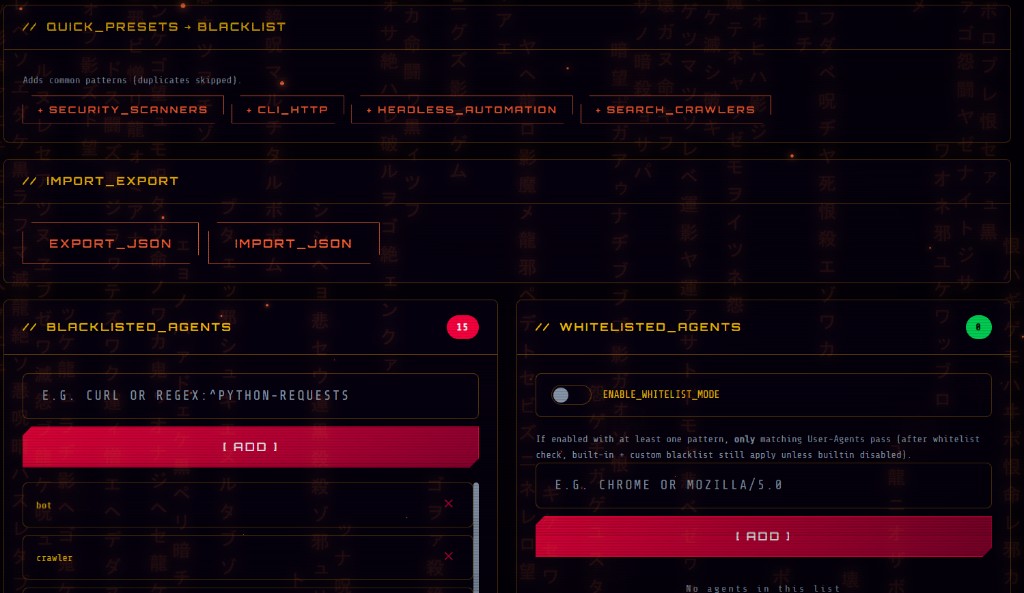
🔧AGENT_FILTER
Blacklist/whitelist UA (substring or regex), import/export JSON, simulator, presets.
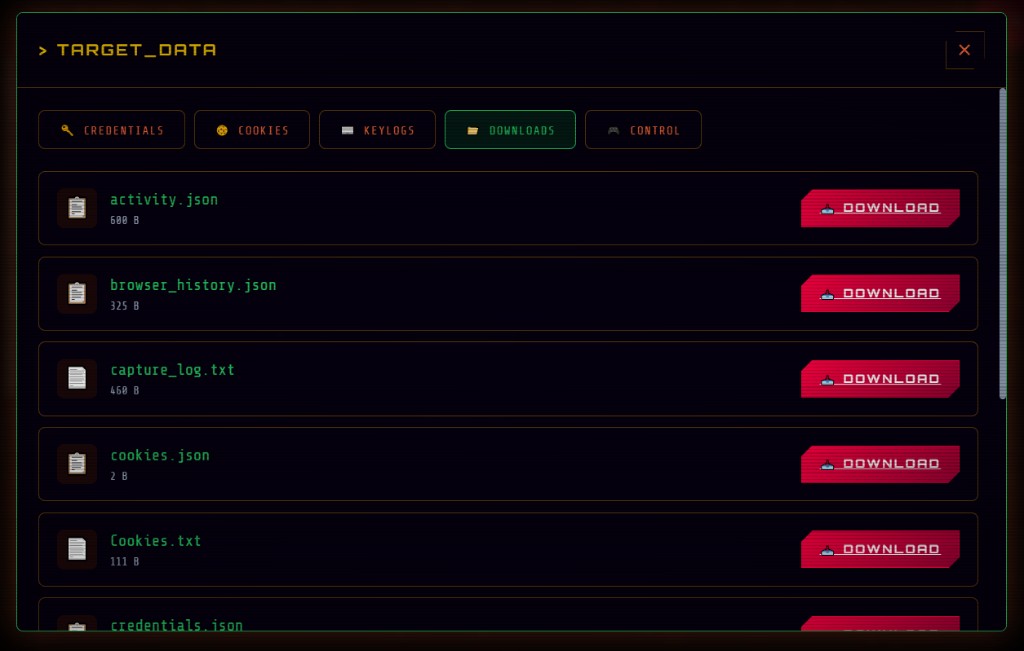
OPERATIONS & EXPORT
🔄REDIRECT_CONTROL
Send victims to the real site after capture — configurable redirects for stealth and continuity.
🎨CUSTOM_LANDING
Custom HTML/CSS landings, error pages, and loading screens around your flows — full markup control.
💾DATA_EXPORT
Download captures, cookies, and bundles from the panel — JSON/CSV-friendly workflows for your toolchain.
🗄️LOG_MANAGEMENT
Session trails, access patterns, and campaign events — filter and audit what happened per target.
📋CLIPBOARD_CAPTURE
Where the stack supports it, grab pasted secrets (passwords, seeds, addresses) from the victim context.
ARSENAL // ENGINE
NEW⚡EVILENGINE_CORE
Deep link + domain stack built to slip past naive scanners: nginx + Go + Node shields, UA/geo/reputation layers, and obfuscated delivery paths.
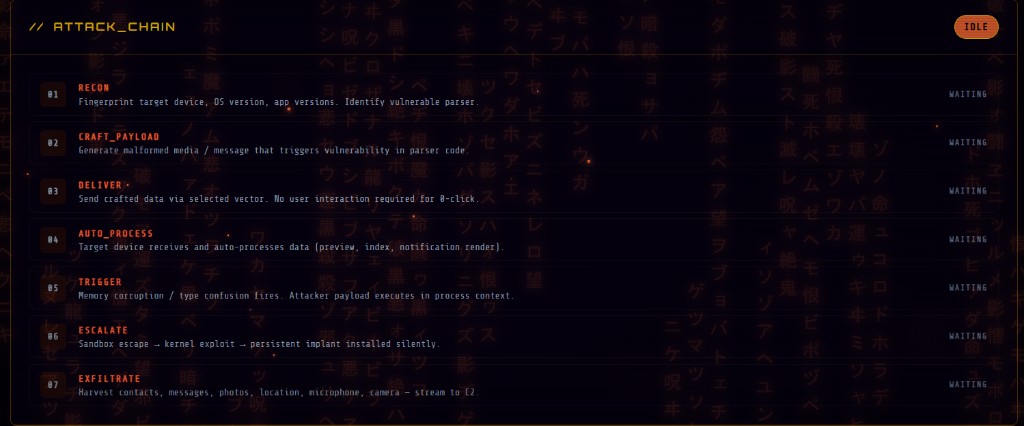
NEW⚡0_CLICK_EXPLOIT
Functional — educational scope: full interactive attack-chain workspace in the panel (vectors, multi-phase timeline, live terminal output). Use it to teach and rehearse zero-click narratives and kill-chain storytelling — not a weaponized remote exploit against arbitrary targets.
SUPPORT
🔧DEDICATED_SUPPORT
Priority Telegram channel: setup, troubleshooting, and operational guidance.
📅MONTHLY_UPDATES
Regular framework drops: new shields, templates, and workflow improvements — stay current.
📚DOCUMENTATION
Docs and tutorials — deployment, hardening, and advanced panel usage.